Switching to Cyber: The Mid-Career Guide to Launching a Cybersecurity Career
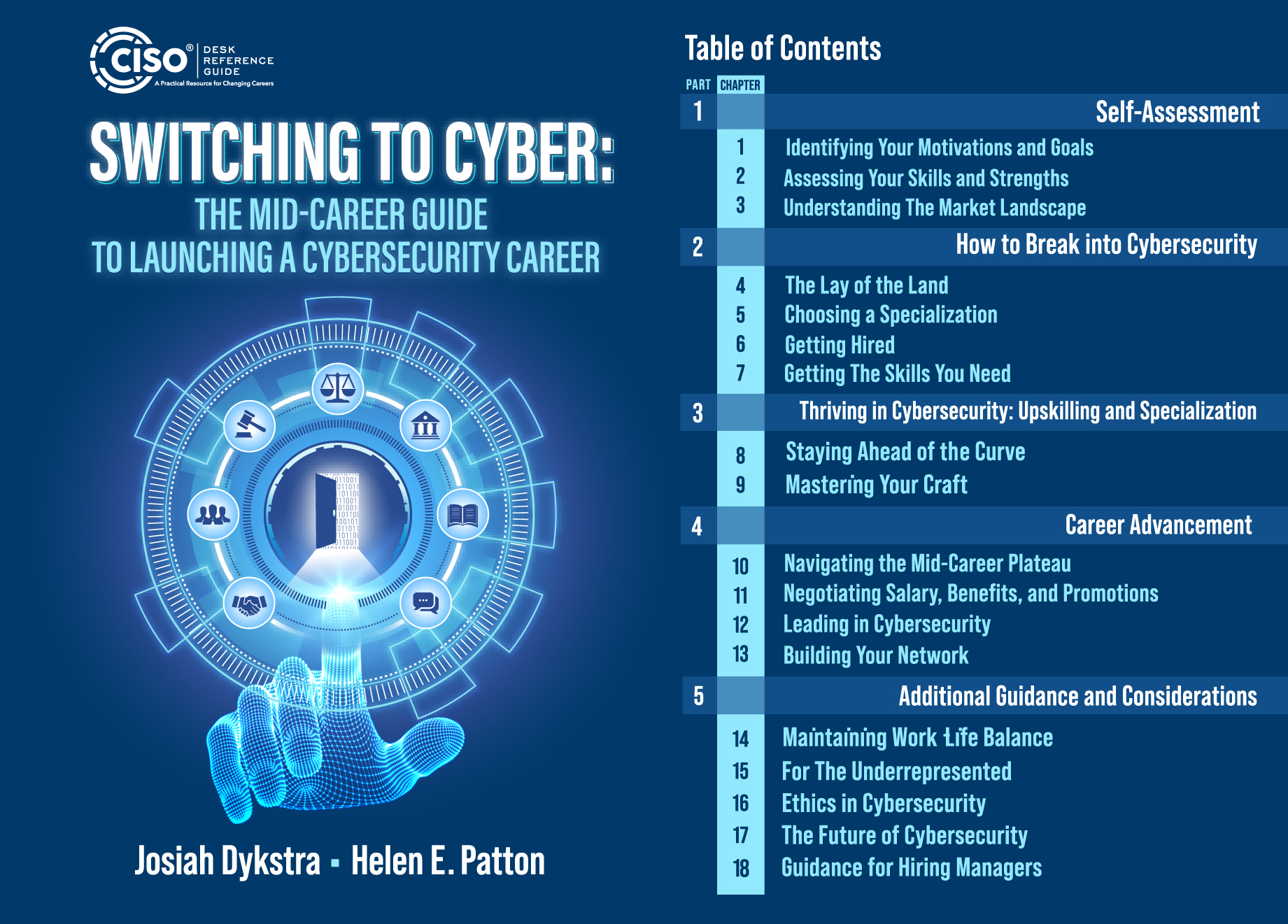
CISO DRG Publishing is proud to announce the publication of Switching to Cyber: The Mid-Career Guide to Launch a Cybersecurity Career, by Josiah Dykstra and Helen Patton.
Switching to Cyber is more than just a career guide, it’s a community of support, filled with real-life stories and advice from individuals who have successfully made the mid-career to cybersecurity.
If you’re ready to break into the exciting world of cybersecurity, you should start your transformation today with Switching to Cyber.
From Dr. Diane M. Jonosek, PhD, Eqs, CISSP and CEO of Janos LLC
“Your prior experience isn’t something you need to overcome. It’s your superpower. The industry is evolving. We need more people who understand how the works works outside of cybersecurity because that’s exactly what we’re trying to Protect.”
Switching to Cyber adds two new authors to our expanding team and joins a growing list of books in our Practitioner Series. It is the essential resource for you as you plan your move to the exciting field of cybersecurity.
Congratulations Josiah and Helen. Well done!







Recent Comments