Switching to Cyber: The Mid-Career Guide to Launching a Cybersecurity Career
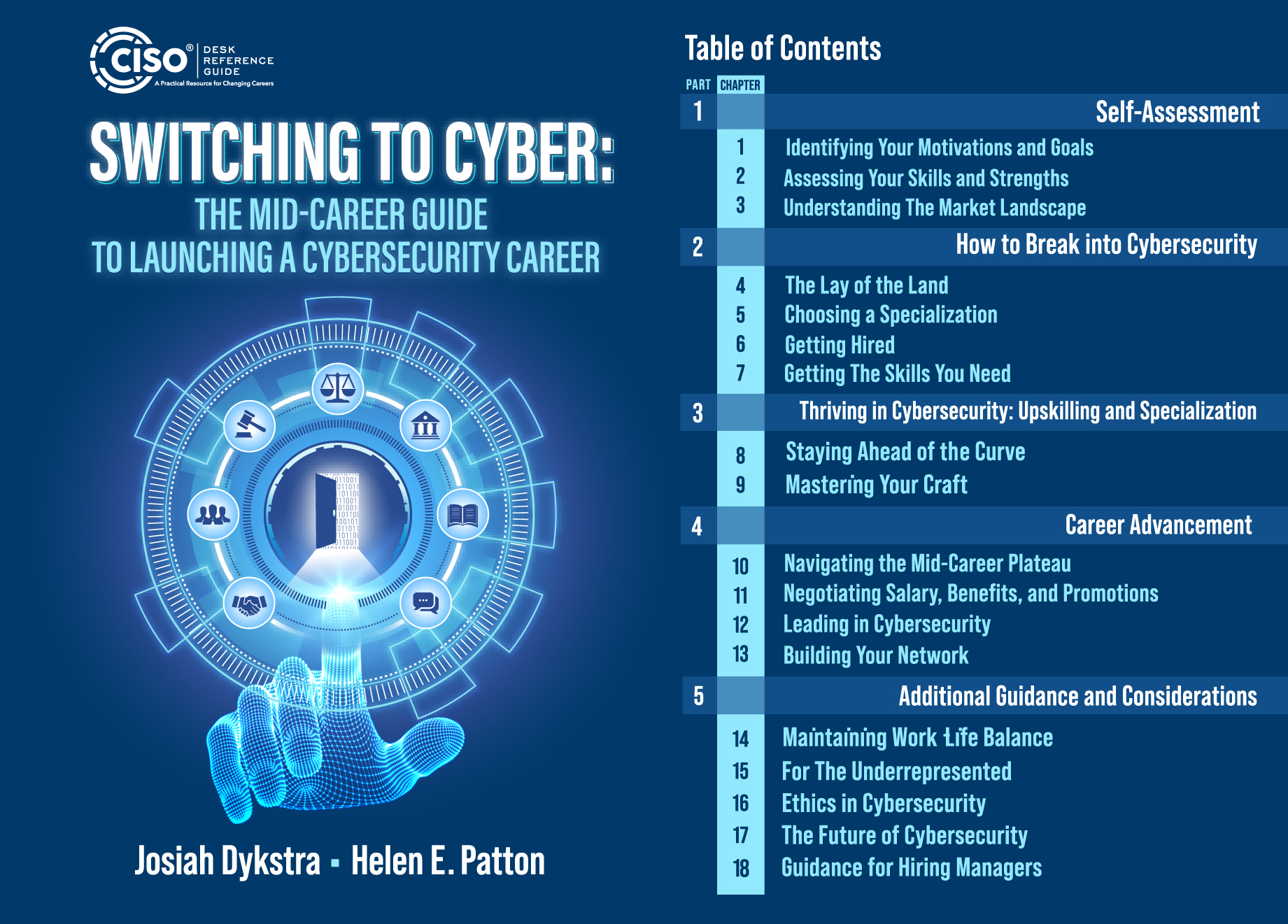
CISO DRG Publishing is proud to announce the publication of Switching to Cyber: The Mid-Career Guide to Launch a Cybersecurity Career, by Josiah Dykstra and Helen Patton.
Switching to Cyber is more than just a career guide, it’s a community of support, filled with real-life stories and advice from individuals who have successfully made the mid-career to cybersecurity.
If you’re ready to break into the exciting world of cybersecurity, you should start your transformation today with Switching to Cyber.
From Dr. Diane M. Jonosek, PhD, Eqs, CISSP and CEO of Janos LLC
“Your prior experience isn’t something you need to overcome. It’s your superpower. The industry is evolving. We need more people who understand how the works works outside of cybersecurity because that’s exactly what we’re trying to Protect.”
Switching to Cyber adds two new authors to our expanding team and joins a growing list of books in our Practitioner Series. It is the essential resource for you as you plan your move to the exciting field of cybersecurity.
Congratulations Josiah and Helen. Well done!
A Comprehensive Guide to Application Security for CISOs
CISO DRG Publishing is proud to announce the publication of the two-volume book on application security: A COMPREHENSIVE GUIDE TO APPLICATION SECURITY FOR CISOs by Yuval Sinay and Nitzan Levi. Volume One: Foundations of Application Security, helps you strengthen your application security approach and stay current with the latest standards, best practices, and emerging trends in secure development. Volume Two: Building and Maintaining Secure Applications builds the foundation laid in Volume One and teaches you how to lead them—across teams, departments, and the entire organization. Both books are available for immediate sale.
Yuval Sinay and Nitzan Levi are uniquely qualified to share their expertise in Application Security. As Head of the Active Cyber Defense (ACD) Department in the Israel National Cyber Directorate (INCD), Yuval has deep experience in the areas of vulnerability research, secure development lifecycle (SDL), cloud security, supply chain, risk management, data protection, cyber regulation, and emerging technologies. Yuval is currently a Ph.D. candidate.
Nitzan is a cybersecurity expert who provides applied consultancy services with a vast background in software development, architecture, application security, risk management, cyber training, and lecturing. He is the Co-Founder & Executive Director at Cybecs and Co-Founder of RedRok.io, an Al-driven platform for continuous threat exposure management. Nitzan is pursuing his Ph.D. in Cyber and Governance, and is also an Authorized Cisco Instructor, ISC2 Authorized Instructor for CISSP, Program Director for CISO at Bar Ilan University, and a Fellow at the International Institute for counter-terrorism (ICT) at Reichman university.
A comprehensive Guide to Application Security for CISOs adds these two terrific new authors to our expanding team and joins Cyber Crisis Response: Leveraging the SONAR Method™ to Accelerate Response and Recovery in our Practitioner Series.
Congratulations Yuval and Nitzan. Well done!
Mastering Third-Party Risk Published

CISO DRG Publishing is proud to announce the publication of Mastering Third-Party Risk: A Practical Handbook for Managing Vendor, Third-Party, and Supply Chain Threats in Every Organization, by Bill Bonney, Chris Forbes, Gary Hayslip, Dr. Andrea Little Limbago, and Matt Stamper.
In Mastering Third-Party Risk, the authors bring together a wealth of expertise from across the risk management spectrum, forming an ideal team to address the complex and urgent challenges of third-party risk. Drawing on their collective experience as practitioners, consultants, and researchers, they deliver a rich blend of insights that both inform and motivate.
As supply chains become increasingly complex, often spanning multiple countries, they become more vulnerable to geopolitical risks and logistical challenges. Unplanned events, such as natural disasters, supplier bankruptcies, trade disputes, and cyberattacks, can lead to significant operational disruptions and economic losses and have profound implications for a company’s financial stability. This book provides a thorough treatment of third-party risk, whether you’re dealing primarily with regional vendors or a complex global supply chain.
Mastering Third-Party Risk adds two new authors to our expanding team and joins Data Privacy Program Guide: How to Build a Privacy Program that Inspires Trust in our Governance Series. It is the essential resource for you as you build or improve your third-party risk management program and is available for immediate sale.
Congratulations Bill, Chris, Gary, Andrea, and Matt. Well done!
How highly effective CISOs lean forward with proactive risk management

No executive wants to be blindsided by risks, and the role of the CISO is more crucial than ever in preventing that. The most effective CISOs run highly effective, risk-focused security programs and are experts at relating technology, digital, and cyber risks to the business and its initiatives.
Sysdig’s latest blog by Matt Stamper, CIPP/US, CISA, CISM, CRISC, CDPSE, QTE dives into how CISOs can effectively manage and communicate digital and cyber risks within their organizations.
Catch it here to learn how to enhance your organization’s cyber risk management strategy: https://okt.to/huK2CQ hashtag#CISO hashtag#Cybersecurity hashtag#RiskManagement
Protect Your Practice and Protect Your Business
CISO DRG Publishing is proud to announce the publication of two new books in the Small Business Series. These are successor books to Bring Your Own Cyber, originally published in 2020. Protect Your Business: A Small Business Guide to Basic Cybersecurity is written for small businesses and Protect Your Practice: Basic Cybersecurity for Healthcare, Legal and Financial Professionals is tailored specifically to small independent offices is professional services.
 |
 |
The eight chapters in these books teach readers the basics. They use plain language to small owners and independent professionals how to become more secure. They include prudent steps readers can take right away to be more secure and every chapter comes with “Pro Steps” to take it to the next level.
Available for immediate sale, Matt, Gary, and Bill congratulate Bill and David. Good work, guys!
Cyber Crisis Response: Leveraging the SONAR Method to Accelerate Response and Recovery
CISO DRG Publishing is proud to announce the publication of Cyber Crisis Response: Leveraging the SONAR Method to Accelerate Response and Recovery, by Andrew Gorecki and Christopher Scott.

In Cyber Crisis Response, Andrew and Chris introduce The SONAR Method™, a proven, proprietary framework they developed through years of being on the front line, responding to cyber crises as the unfold. Andrew and Chris have lived in the trenches of crisis response, this book describes many of the common pitfalls and their battle-tested solutions. There is no better way to learn than to do it yourself, but understanding the lessons others have learned is essential to help you prepare.
Crisis response is a complex undertaking that requires the coordination of multiple, often conflicting, activities. No playbook replaces experience and critical thinking. Using The SONAR Method will help any practitioner:
- Understand how to stabilize an environment during a cyber attack
- Learn how to organize the team and resources needed to resolve the situation
- Facilitate negotiations across a wide variety of stakeholders involved in the crisis
- Discover how to effectively articulate and communicate the situation and resolution to a broad range of stakeholders
- Develop the specific action plan required to remediate and recover from the incident
With a foreword written by George Kurtz, President/CEO and co-founder of CrowdStrike, Cyber Crisis Response is the essential resource for you to up your game and respond with confidence when the inevitable cyber crisis strikes.
Available for immediate sale, Matt, Gary, and Bill congratulate Andrew and Chris. Well done, gentlemen!
What is the interview process like for CISOs?

In this episode, Host Ron Eddings catches up with repeat guest, Gary Hayslip, CISO at SoftBank Investment Advisors and co-author of CISO Desk Reference guide. Gary explains that the varied nature of his current CISO role contrasts with the broader industry trends. He discusses how that nature plays into the CISO hiring process and career path, as well as how his books are helping to bridge the gap among professionals.
Impactful Moments:
00:00 – Welcome
00:59 – Introducing guest, Gary Hayslip
01:38 – The Path to Becoming a CISO
08:04 – CSO vs CISO
10:47 – “I’m firing you…”
15:03 – Interviewing for the CISO role
17:56 – Join Our Mastermind
18:39 – Being ‘Mr. Maybe’
21:41 – CISO- A Day in the Life
24:50 – Using Books to Pave the Way
Links:
- Connect with Gary on LinkedIn: https://www.linkedin.com/in/ghayslip/
- Check out Gary’s Books on Amazon
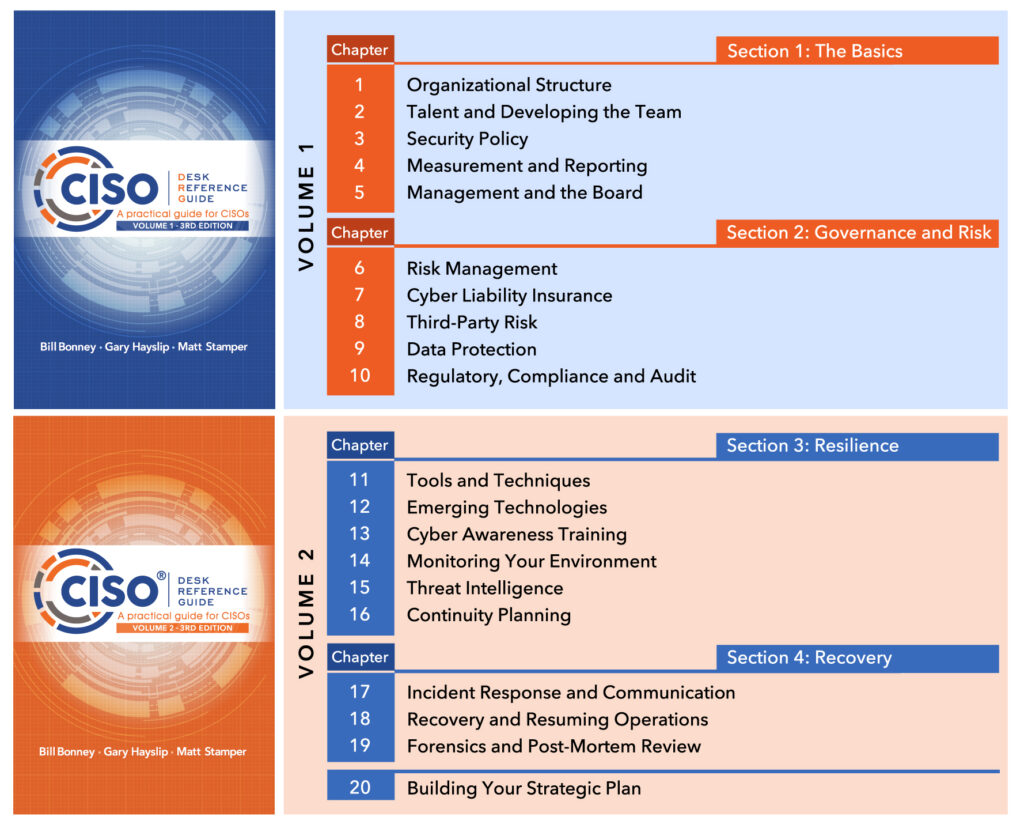
Third Edition of the CISO Desk Reference Guide, Volume 1 and 2 released together
CISO DRG Publishing is pleased to announce publication of the third edition of the CISO Desk Reference Guide: A Practical Guide for CISOs, Volume 1 and 2, by Bill Bonney, Gary Hayslip, and Matt Stamper, co-founders of CISO DRG Publishing. We wrote the Guide as a foundational reference for CISOs. The third edition has been updated with new insights and updated references along with new chapters on emerging technologies (Chapter 12 in Volume 2) and cyber liability insurance (Chapter 7 in Volume 1).
As a guide written specifically for CISOs, we hope Volumes 1 and 2 of the CISO Desk Reference Guide become trusted resources for you, your teams, and your colleagues in the C-suite. Congratulations, Bill, Gary, and Matt, and thank you for updating this important work.
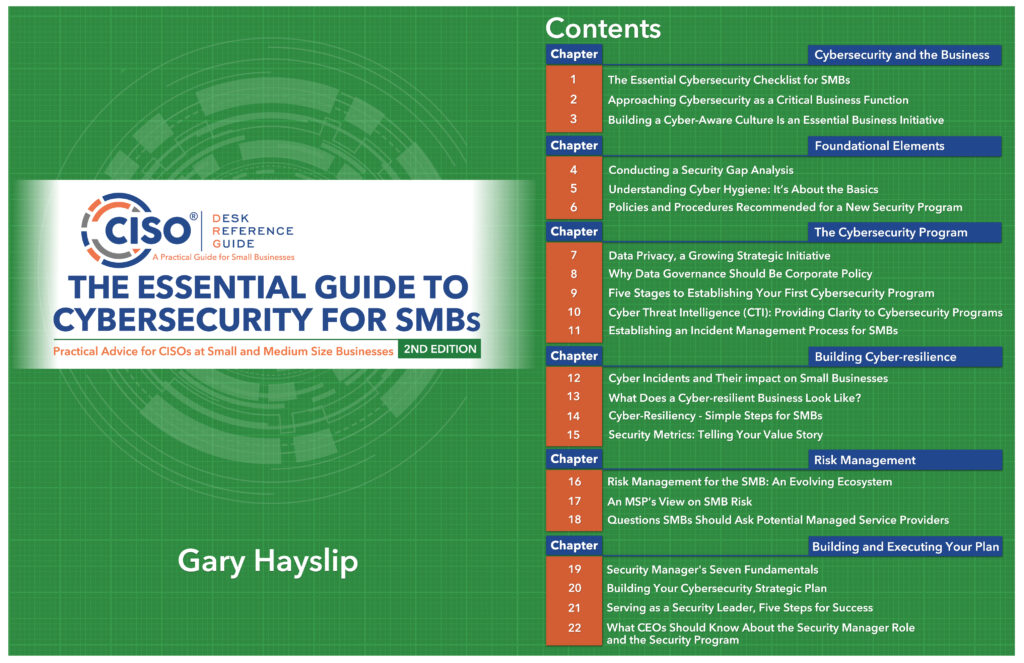
Second edition of The Essential Guide to Cybersecurity for SMBs: Practical Advice for CISOs at Small and Medium Size Businesses
CISO DRG Publishing is pleased to announce publication of the second edition of The Essential Guide to Cybersecurity for SMBs: Practical Advice for CISOs at Small and Medium Size Businesses, by Gary Hayslip, co-founder of CISO DRG Publishing.
Gary wrote the first edition of The Essential Guide to Cybersecurity for SMBs in February of 2020, and this book has been a wonderful resource to cybersecurity professions and small and medium size businesses. If the three years since the first edition came out have taught us anything, it’s that smaller firms now have just as big a target and the experience Gary shares has never been timelier.
The second edition has been updated with new insights and updated references. Congratulations, Gary, and thank you for updating this important work.
SPEAKERS ANNOUNCED: CYBER DEFENDERS @ RSA CONFERENCE
InfraGard National Members Alliance is pleased to announce our instructors and speakers for Cyber Defenders, presented in partnership with RSA Conference.
During this immersive two-day workshop, receive briefings from the FBI’s cyber and counterintelligence divisions, explore cyber laws shaping the regulatory environment, and discuss what constitutes ‘reasonable security’ with two experts who literally wrote the book on the subject. Sessions focused on leveraging threat intelligence and implementing effective insider-threat programs will provide attendees with practical steps they can take to manage risk in their organizations. #InfraGard
View the agenda at https://lnkd.in/gAhzbaRj
Register by the March 10 deadline at https://lnkd.in/gaKiiJZG


