The CISO Desk Reference Guide, Volume 1, 3rd Edition is the greatly anticipated update to the first volume of the highly respected two-volume set written by experienced practitioners and intended for recently hired or promoted Chief Information Security Officers (CISOs). These easy-to-use guides are also perfect for individuals aspiring to become CISOs, as well as business and technical professionals interested in the topic of cybersecurity. Those with the titles Chief Technology Officer (CTO), Chief Information Officer (CIO), and Chief Privacy Officer (CPO) will gain critical insights, and members of the board of directors and other executives responsible for information protection will find them invaluable.
As a desk reference guide written specifically for CISOs, we hope this book and its companion CISO Desk Reference Guide, Volume 2, become trusted resources for you, your teams, and your colleagues in the C-suite. The different perspectives offered by the authors can be used as standalone refreshers, and the five immediate next steps for each chapter give the reader a robust set of actions based on roughly 100 years of relevant experience that will help you strengthen your cybersecurity programs.
Description
The CISO Desk Reference Guide is constructed as a two-volume set. For the third edition, we made some key changes to how we arranged the material to provide what we believe is a better flow from topic to topic. Chapters are slightly reordered, and a couple of chapters have moved from one volume to the other. Most chapters still follow the same format, including an introduction, separate essay by each of us, and a summary. The introduction highlights the different perspectives we bring to the chapter and sets the tone with the questions we used to frame our thoughts. The summary pulls together the key points and immediate next steps for you and your team, making this a practical guide for CISOs. Finally, for the summary and key action for Chapter 20, we challenge you to build your strategic cybersecurity plan. Chapter 7 (Cyber Liability Insurance), Chapter 12 (Emerging Technologies), and Chapter 20 (Building Your Strategic Plan) each present a unified essay on the topic.
Volume 1 addresses what we call the basics of the CISO role, along with critical governance functions. Section 1: The Basics covers the organizational structure, developing the team, security policy, measurement and reporting, and working with senior management and the board. Section 2: Governance addresses the topics of risk management, cyber insurance, third-party risk, data protection, and security compliance and audit. One of the most essential governance concepts is how the CISO helps management and the board understand the full scope of risk and the techniques used to render the risk acceptable to ensure that the organization is a going concern.
Integral to the governance discussion is a robust treatment of risks posed by third parties, vendors, and suppliers. The ecosystems we build today are so interconnected with partners. Unfortunately, these interconnections create creases in our cybersecurity defenses and force us to entrust our data to many other parties. While no good CISO wants to slow the pace of change, every good CISO recognizes and helps the organization understand that the pace of technology change combined with the expanding network perimeter exposes us to enormous risk.
Here is the layout for the two-volume set.
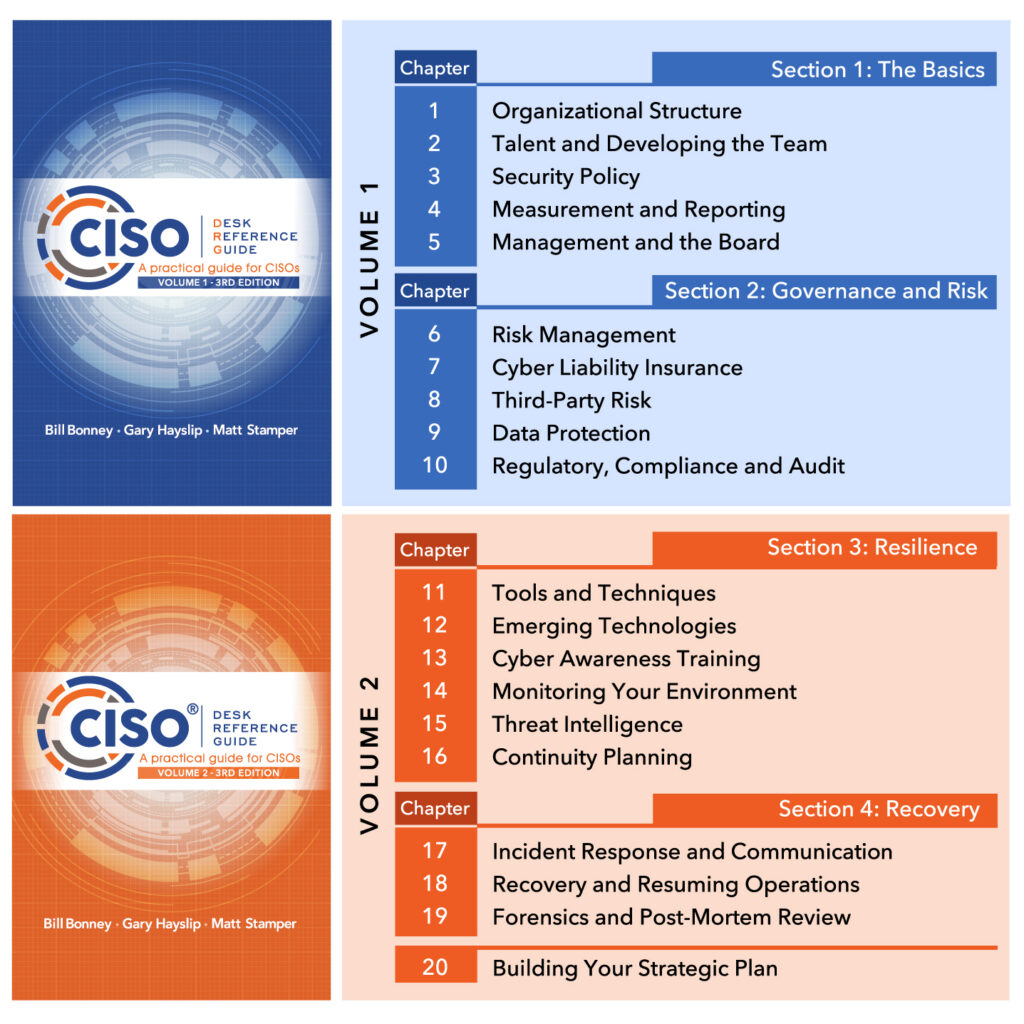
The order of the essays within each chapter follows the arc of our differing backgrounds and perspectives. Bill Bonney’s essays lead off each chapter and provide a high-level view that reflects his background in the finance industry and the structured governance that comes with working in a highly regulated industry. Matt Stamper’s essays come next, and his perspective on simultaneously providing services to many customers provides insight into a highly programmatic approach. Finally, Gary Hayslip’s essays finish each chapter, and his vast experience in the trenches as a hands-on cyber expert provides you with a treasure trove of lists and lessons that you can repeatedly reference. We deviate from this approach for Chapters 7, 12, and 20, where we provide a single, unified essay.
Dr. Winnie Callahan Review
Review of the book: CISO: Desk Reference Guide
A Practical Guide for CISOs
Publisher: DRG Joint Venture Publishing, 2016
Authors: Bill Bonney, Gary Hayslip, Matt Stamper
By:
Winnie Callahan, EdD
Director, University of San Diego Center for Cyber Security Engineering and Technology
The book, CISO: Desk Reference Guide; A Practical Guide for CISOs is an amazing effort to assist new CISOs or CISOs in mid-size companies to better understand their respective roles, but it actually provides a plethora of in-depth “how tos” and “whys” from the vast wealth of experiences enjoyed by the three authors.
The book is easy to read and is divided into nine distinct chapters each addressing a major issue, concern or responsibility inherent to the role of a CISO. It is not a directive nor is it a textbook designed to provide the reader with a credential. Rather it is exactly what a CISO needs when confronted with the day to day demands placed upon the person brave enough to try a fill some extraordinarily large shoes: the person expected to have a super technical background, but must also understand cybersecurity, laws and policies, have a clear focus on regulations, be a proven leader and also be a “great communicator” to the CEO but often to a Board of Directors as well. (Perhaps when a CISO is hired and/or appointed, one should also receive a Superman costume …. He or she just may need it.)
Realistically, the Superman attire is less likely to be necessary with this volume of guidelines, concrete examples and a concise summary of such valuable information as the NIST framework and the SANS descriptors for handling risk, as examples.
The book is unique, as the reader gets the opinion on each topic from the three authors independently. For the reader, it’s like having a private conversation with experts in the field on the readers’ timeline … in short, when really needed. (This could be during business hours, over the weekend or during the “heat of a crisis.”)
The layout of the book follows closely the rules of public relations: tell the public what you’re going to tell them, then tell them more than once using different techniques and then summarize what you told them. The book also invites contact with the author(s) if you still need more clarity. What a deal!
Each chapter has an introduction, then three different opinions on the topic, one by each author from a “different experience perspective.” Each chapter is rich in explanation, many with charts and graphs. And each chapter concludes with a summary of what the chapter provided.
Whether you’re trying to understand your role better, figure out how to develop policies to ensure the protections your organization requires, desperately need to review the NIST Incident Response Guide, or just validate some steps you plan to take in working with your leadership team, this guide truly has it all.
One of the major criticisms often voiced regarding standards and regulations is that “one size does not fit all.” Frequently, though experts are supportive of the need for standards and the fact that having some are very helpful, they often express dismay that standards are blind to context … this book is exactly what is needed to take that challenge head-on. Again, three differing opinions from three different perspectives reflecting the best and worst of the issues most CISOs encounter … only the type of environment is different and thus, the approach and needs to solve and address the issues will no doubt vary.
As this review concludes, it is important to state that the Appendix at the end of Chapter Nine on Policy is, even as a stand-alone, incredibly valuable as it exemplifies different type of Policies. The reader will also find the Bibliography of great value if wanting to dig more in depth on a given topic. Though the subject is dynamic and fits into the category of “always changing,” the basics of the observations and lessons learned will NOT lose their value to the practicing professional. At the least, it helps clarify the thought processes and the potential evolution to any new applications that will be evident in the future.
In closing, I would encourage those aspiring and or existing CISOs to invest in this book. I would also recommend that universities who are attempting to prepare well-educated cyber professionals for their roles in the Cyber domain to make sure this book, and hopefully subsequent volumes, known to and available for their students. You can’t get much better than a practical, easy to read reference for those times when an answer or validation of a plan would lower one’s stress level and help our corporations, government agencies and our nation as a whole do a better job of protecting assets.
CISO Online Review
A practical guide for CISOs belongs on the desk of every Chief Information Security Officer and wannabe.
Are you an aspiring, recently hired or promoted CISO looking for the definitive how-to guide for your position? Look no further. An experienced CISO along with two security subject matter experts have authored a comprehensive modern day text — ‘CISO Desk Reference Guide: A practical guide for CISOs‘ — which covers risk management, compliance, audit, IT security disciplines, cybersecurity extending to IoT (internet of things) devices, cyber insurance, staffing, board concerns, and everything in between.
The three authors — Bill Bonney, Gary Hayslip, and Matt Stamper — state their decision to write the book came from the shared realization that the dramatic escalation in cyber threats was not going to peak any time soon. A recent report from Cybersecurity Ventures aligns with their thinking — and predicts cybercrime damages will cost the world $6 trillion annually by 2021, up from $3 trillion last year.
(Disclaimer: Steve Morgan is founder and CEO of Cybersecurity Ventures.)
Hayslip brings direct CISO experience to the book. He is deputy director, CISO for the City of San Diego, Calif. — which has more than 1.37 million people, and is the eighth largest city in the United States and the second largest in its home state. He advises the City of San Diego’s executive leadership consisting of Mayoral, City Council, and 40+ city departments and agencies on protecting city government information resources. Hayslip oversees citywide cyber security strategy and the enterprise cyber security program, cyber operations, compliance and risk assessment services.
The CISO Desk Reference Guide is suitable material for security chiefs at Fortune 500, global 2000, and mid-sized corporations, as well as security leaders at U.S. federal agencies, state and local governments, universities, and non-profits. CIOs and senior IT staff at small to mid-sized firms with and without CISOs will also benefit from the soup-to-nuts security guidance found in the book.
The rubber hits the road in chapter 2, which covers regulatory, compliance and audit – a particularly gnarly topic which leaves many new CISOs wondering where to begin. The authors explain what regulatory requirements are, how to engage with auditors, and how to make audits effective. The chapter also speaks to legislation, which is changing cybersecurity… not something immediately obvious to most CISOs.
A severe cybersecurity workforce shortage has left CISOs and corporate IT security teams shorthanded and scrambling for talent while the cyber attacks are intensifying, according to the recent Cybersecurity Ventures report. Corporations are responding by placing some or all of their IT security into the hands of third parties. The IT security outsourcing segment recorded the fastest growth (25 percent) out of the entire cybersecurity market last year, according to Gartner. Outsourcing security introduces a whole new risk for enterprises — choosing the right third party which has the cyber defenders, cyber operations, and security platforms to effectively combat an increasingly hostile threatscape. The CISO Desk Reference Guide devotes an entire chapter to third-party risk — including eight risk factors to assess with vendors including:
- Operational Risk
- Privacy Risk
- Reputation Risk
- Security Risk
- Regulatory Risk
- Revenue Risk
- Financial Risk
- Service Risk
A careful read through these eight points in the CISO Desk Reference Guide is sure to make outsourcing any aspect of security a much less risky proposition for CISOs who are leaning in that direction.
The book is worth its weight in gold for Hayslip’s overview on Cybersecurity Tools and Techniques. He shares that if there’s one thing he has learned as a CISO, it’s that if you want to be effective you must work to build trust with the organization’s stakeholders and make the case that cybersecurity is a value proposition, a service that all business channels should leverage to be competitive. Then he dives into what readers have been waiting for — an experienced CISO’s recommendations around security policy, incident response, data back-up, security awareness training for employees, patch management, anti-virus and malware protection software, vulnerability scanning, desktop encryption, wireless network security testing, email security, and more.
There’s still 10 days left until the end of summer 2016… so it’s not too late to make the CISO Desk Reference Guide your summer read.
Palo Alto Networks Review
We modeled the Cybersecurity Canon after the Baseball or Rock & Roll Hall-of-Fame, except for cybersecurity books. We have more than 25 books on the initial candidate list, but we are soliciting help from the cybersecurity community to increase the number to be much more than that. Please write a review and nominate your favorite.
The Cybersecurity Canon is a real thing for our community. We have designed it so that you can directly participate in the process. Please do so!
Executive Summary
Every profession has desk references that practitioners can use as go-to guides for tactical information. For information security professionals, CISOs and those on the CISO track, the
CISO Desk Reference Guide: A Practical Guide for CISOs is an excellent example of such a guide.
Review
While the classic prepare 3 envelopes joke revolves around CEOs, it’s quite appropriate for a CISOs as well. For many, their career path is a slow and steady one whereby they deliberately progress toward attaining that role. For others, who quickly obtain the role due to a major security breach, envelope #3 must often be opened immediately.
In the CISO Desk Reference Guide: A Practical Guide for CISOs (CISO DRG 978-0997744118), authors Bill Bonney, Gary Hayslip and Matt Stamper have written a tactical guide that can help the soon-to-be or new CISO get up and running. Each of the three has been in the information security space for decades, and all of them bring their experience from the trenches to every chapter.
For CISOs who find themselves in that position, they’ve entered it as a key entity in an organization. For those who have come into the role suddenly, it’s important to note that poor information security controls can bring an organization to its knees. In the book, the authors share their knowledge and provide real-world experience, showing current CISOs – and security managers with aspirations to be – how to function most effectively in the CISO role.
A recurrent problem for books with multiple authors is that the end result often lacks consistency and is simply a collection of different essays without a unifying theme. The authors here do an admirable job of avoiding that. Each chapter is clearly identified by who the specific author is. A benefit to the approach here is that each of the authors brings his specific style to information security, such that the reader ends up with a broad and multifaceted methodology on the topic.
The nine chapters in the book cover the entire range of the information security lifecycle; from regulatory issues to data classification, reporting to the board, tools, policies and more. The three authors are battle-tested professionals with real-life expertise that they bring to every chapter.
The previous point is not a trivial one as information security is not monolithic. There is certainly no single way to do information security. By learning the topic from the best and the brightest, information security practitioners and CISO-hopefuls can ensure they will ultimately be successful in their endeavors.
As mentioned above, many books with multiple authors suffer from a lack of consistency and message. This book doesn’t suffer from that. And in fact, each author brings a slightly different approach to the various topics. This is an important point, as there is certainly no one size fits all when it comes to information security.
Of course, an effective CISO can’t rely on any single book. And if they tried, that book would need to be about 2,500 pages long. But for those looking for a go-to reference when the CxO urgently calls, it would be a good idea for any information security professional to have a copy of the CISO Desk Reference Guide handy. It’s an excellent desktop reference – and an indispensable one, at that.
Conclusion
The CISO Desk Reference Guide: A Practical Guide for CISOs is an excellent desk reference that information security professionals, from managers to CISOs, will find of value. It’s full of practical, real-world experience and sage advice, making it an excellent candidate for the Cybersecurity Canon.
Praise for the Book
“CISO Desk Reference Guide is a one-of-a-kind reference – well-structured that should be easily understood by techies and non-techies alike (especially the finance and legal types – who probably need this more than the CISOs). Great work!”
RADM (Ret) Kenneth D. Slaght
Co-Chair and President
Cyber Center Of Excellence
“I strongly recommend this unique, applicable, and much needed CISO guide. The three authors, all proven CISOs as well as leaders, have taken a very unique approach to creating the CISO Desk Reference Guide, tackling real world issues, but not by each taking a section and sharing their knowledge, but by all three providing relevant input on each topic. Their differences in viewpoints, experience, and writing styles provide more than a single perspective or solution; they provide a rich and diverse foundation for the reader to process information and draw conclusions that best meet their needs, honing critical thinking!
I recommend this book for experienced CISOs who want fresh thinking on current topics, new CISOs who want to learn from the best, or others in information security and risk management who desire a greater foundation on the complex world of CISOs.”
Todd Friedman
Chief Information Security Officer
ResMed
“This is an excellent desk reference for new and established CISOs who are increasingly challenged by advancing threats, standards, and regulations. The organization of the book, where each of the three authors provide their own thoughts on many important topics, illustrates the fact that the challenges faced by CISO don’t have single, pat answers. Readers can consider the book to be written mentorship by three active CISOs.”
Peter H Gregory
Executive Director, National Security Advisory Firm
“Essential reading for both aspiring and incumbent Chief Information Security Officers, the CISO Desk Reference Guide fills a critical gap in the information security common body of knowledge.
The Chief Information Security Officer has emerged as a key role in forward-thinking organizations that are keenly aware of the existential threat that cyber risks now pose. The authors of the CISO Desk Reference Guide grasp that reality and use their many years of experience to provide a ton of practical advice about how to function effectively in this role.
The unique multi-author approach of the CISO Desk Reference Guide has produced a wealth of insight into the complex and challenging role of Chief Information Security Officer, a role that increasingly anchors organizational risk management in all things cyber and digital.
From the excellent discussion of the evolving CISO role and how best to embed it in the organization, to fundamentals like data classification and controls, to advice on tools and techniques, the CISO Desk Reference Guide delivers multiple perspectives on the foundations of organizational cybersecurity.
I wholeheartedly recommend the CISO Desk Reference Guide to anyone who is or wants to become a Chief Information Security Officer.”
Stephen Cobb, CISSP
Senior Security Researcher, ESET North America.
“The CISO Desk Reference Guide” is a useful tool written with a unique tri-perspective of three authors. The diversity in perspectives is powerful in that it demonstrates there is never just one solution to any situation, yet it provides great examples and things to ponder for the reader.”
Gabriele Benis
Former Vice President of Audit
Intuit, Inc.
“The field of Information Security & compliance is complex at the very least. And the job of “CISO” still a mystery to most boards and CEO’s. However, three icons in the cybersecurity community, Bill Bonney, Gary Hayslip, and Matt Stamper took a very complex subject matter and through the use of what they call “Tri-Perspective” take on each practical subject matter, and truly makes it a “CISO’s Desk Reference Guide”! The call to action with the five immediate “Next Steps”. Will be a great comfort to those new CISO’s that walk into the job the first day, “with a deer in headlights mentality”! Not because they are not qualified but because the job of CISO, in most companies is still being defined. And this desk reference book will be a great resource for the CEO, Board and CISO.”
David W. Rooker, CISSP
Chief Information Security Officer
Actian Corporation
“Bill Bonney, Gary Hayslip and Matt Stamper have managed to successfully explain the role of the CISO and have provided insights and straightforward, practical suggestions for strengthening your cybersecurity programs. This book should be required reading for every CISO or those aspiring to become one.
The best book ever written on the role of a modern day CISO. Ground breaking with insights and advice on every page, The CISO Desk Reference Guide is a major contribution to the industry.”
Jane Frankland
Founder of Cyber Security Capital, Board Advisor ClubCISO
“…The book is unique, as the reader gets the opinion on each topic from the three authors independently. For the reader, it’s like having a private conversation with experts in the field on the readers’ timeline … in short, when really needed….
Frequently, though experts are supportive of the need for standards and the fact that having some are very helpful, they often express dismay that standards are blind to context … this book is exactly what is needed to take that challenge head-on.” (read Dr. Callahan’s extensive review here)
Winnie Callahan, EdD
Director, University of San Diego Center for Cyber Security Engineering and Technology
“This is a fantastic resource for every security professional seeking to improve their skills and their careers. The structure of the guide works extremely well for readers who want a deep-dive and those who are seeking just the answers or a quick refresher with the key points at the end of each chapter. It’s rare to find a treasure trove of knowledge like this. I look forward to Volume 2.”
Vickie Miller
Chief Information Security Officer
FICO
“Tremendous value. Insightful and impactful for any organization, any executive and any board. Ties the criticality of managing risk to the need to be a part of the core business in a mature and commonsense way. This should help organizations futureproof their business with concepts and frameworks that are relevant today and for tomorrow.”
Mark Wales
Vice President, 30+ year industry veteran and board member of the Workforce Institute