The Information Security or Cybersecurity organization has its origins in two different but related corporate functions. Network security, which largely grew out of the network infrastructure and systems administration disciplines, and what is commonly referred to Governance, Risk and Compliance (GRC) which often traces its roots to regulatory compliance, internal audit and program management. While network security was focused on protecting the network from unsanctioned activity, GRC was tasked with assessments and demonstrating compliance with standards, frameworks, and contracts. These two functions often worked hand-n-glove, defining proper hygiene, implementing controls, assessing network health, and monitoring for compliance.
Third-party risks grow greater and more complex as the number of third parties we deal with grows and the complexity of our supply chains increases. In Mastering Third-Party Risk: A Practical Handbook for Managing Vendor, Third-Party, and Supply Chain Threats in Every Organization we look at several dimensions of third-party risk with a stellar team of experts. Whether it’s the problems small companies face managing the risk from a handful of regional vendors, larger concerns with a multitude of third parties providing a wide range of services or multinational corporations managing global supply chains. We look at much more than security and we look into the future to help practitioners understand how to deal with climate risk, geopolitical risk, and technology risk, including artificial intelligence.
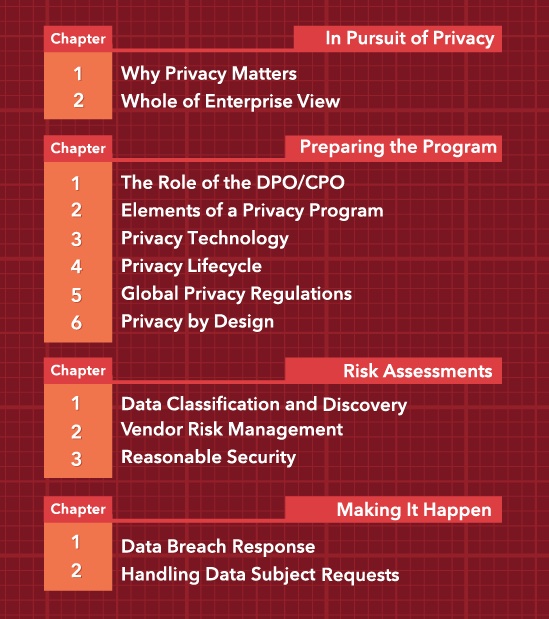
The Data Privacy Program Guide: How to Build a Privacy Program that Inspires Trust is intended for privacy professionals including the Chief Privacy Officer (CPO), Data Protection Officer (DPO), and privacy program managers, as well as privacy attorneys, the CIO, CISO and anyone tasked with managing risk related to privacy laws, compliance regulations and reputation. Recognizing that while a younger sibling in many organizations, the role of the CPO is rapidly maturing, acquiring a larger and larger portfolio, both for customer advocacy and data privacy regulations, and is inexorably tied to information security.